Leave no trace: Tips to cover your digital footprint and reclaim your privacy

Alex Castle@atcastle
Apr 16, 2014 3:30 AM
Privacy is at a premium. Whether it’s the NSA, a hacker cabal, or corporate marketers, someone is looking over your shoulder every time you use your PC.
You can minimize your exposure, though. Whether you’d just like to keep your Web browsing under wraps or you want to obliterate all evidence of digital activities, follow these tips to stay on guard and off the grid.
Conceal your Internet activity
Covering your tracks on the Web starts with your browser’s private browsing feature. Internet Explorer, Chrome, and Firefox each have this functionality, which prevents the browser from keeping a history of the pages you view. You can enable private browsing from the main menu—in Internet Explorer it’s called InPrivate Browsing, in Chrome it’s Incognito mode, and in Firefox it’s simply referred to as a Private Window.
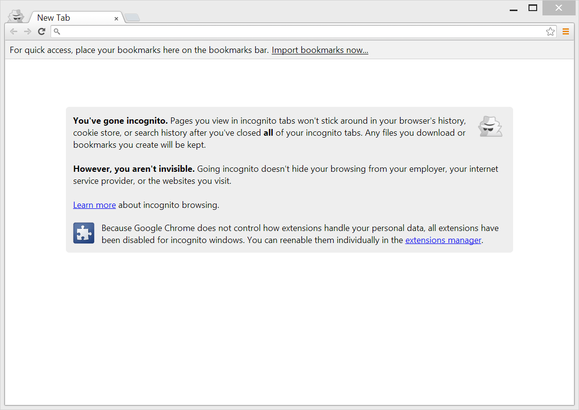
Private browsing features, like Chrome's Incognito mode, prevent Web browsers from recording your history.
Note that private browsing won’t remove every trace of your Internet activities. Any files you save will remain. Private browsing also doesn’t do anything to obscure your Web traffic from the server’s side. Websites you visit will still have your IP address, and any unencrypted data you send is as susceptible to interception as it would be in a normal browser session.
A more covert option is to use private browsing in conjunction with Sandboxie, an application that prevents other programs from saving any data to your disk (including malware that might try to sneak in from the Internet).
Finally, there’s Tor, a network that allows you to browse the internet completely anonymously. While you’re running the Tor software, any outgoing or incoming network traffic is first bounced among many other computers that people have set up to act as nodes in the Tor network. Any sites you visit won’t know your IP address (which can be used to find out where you live), and anyone listening in on your outgoing traffic (including your ISP) won’t be able to tell what sites you’re visiting.
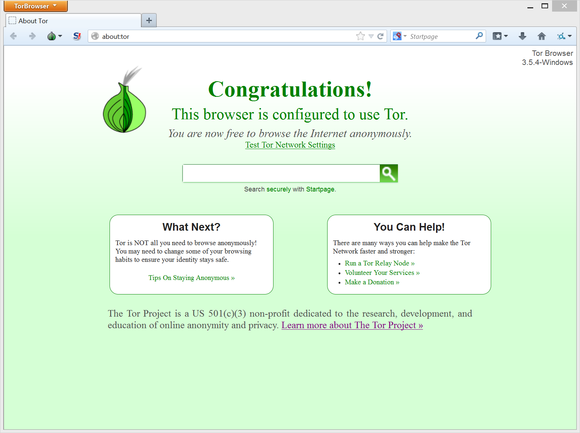
Tor lets you browse the Web anonymously--and very slowly.
But while Tor may be the biggest weapon in the battle to protect your privacy, it’s certainly not the fastest. All that server-bouncing slows down your browsing considerably. Unless you’re a dissident in a repressive regime, or someone else with a life-or-death need for Web anonymity, you may well find that Tor is more security than you actually need.
Put your data on the down low
The next step is to protect the personal data on your PC.
You should have unique user accounts with passwords set up for each person who uses your computer, including guests. (Windows guest accounts have lesser privileges.) By default, any file in the C:/Users directory (which includes My Documents, My Photos, and all related folders), is accessible only to the user account that created it. It’s not airtight security, but it will reduce access to your files.
User accounts alone won’t protect your private data from someone determined to get at it. To make your hard drive snoop-proof, you need to encrypt it. The easiest way to do this is with Bitlocker, the full-disk encryption built into the Ultimate and Enterprise editions of Windows 7 and Vista, as well as in the Pro and Enterprise versions of Windows 8. By default Bitlocker isn’t enabled, but you can turn it on by going to Control Panel > System and Security > Bitlocker Drive Encryption. Encrypting your whole drive will make it completely inaccessible to anyone who doesn’t have your Windows user password.
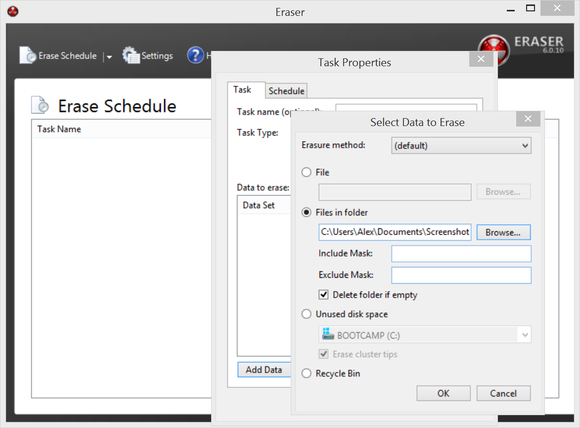
Eraser overwrites your data, making it iimpossible to recover.
If you don’t have Bitlocker, you can still get free full-drive encryption with TrueCrypt, which secures your files with military-grade protection. Like Bitlocker, it can be used to encrypt your whole hard drive or just a subset of files. Files locked with TrueCrypt aren’t just inaccessible—they’re invisible to anyone who doesn’t have the password for the containing volume.
Don’t assume a deleted file is gone for good. Windows doesn’t actually remove the data from your hard drive, it simply gets rid of the bit of your file system that points to the file. Even if you remember to empty your computer’s recycle bin, trashed data can frequently be recovered with software like Recuva. There are many utilities available to destroy a file. A program like Eraser, for instance, actually overwrites that data on your hard drive, ensuring that it can never be resurrected.
Corral clandestine activities to a private OS
Many privacy pitfalls boil down to the fact that Windows is a complicated operating system, and it’s difficult to keep track of all the nooks and crannies into which your data is being sorted. To eliminate evidence of your activities, the best option is to work in an operating system entirely separate from your regular one.
One easy way to do this is with virtualization. Using free software like VirtualBox, you can run a separate Windows or Linux computer in a window on your PC. Virtualization sets up a wall around the virtual computer, so nothing you do on the PC in VirtualBox can leave any files on your normal Windows file system. If you’re really paranoid, you can even keep the VirtualBox data in a TrueCrypt volume, so that nobody but you can see it.
Finally, if nothing so far in this article is enough security for your needs, there’s one last piece of software that provides absolute privacy. It’s called Tails OS, and it’s for when you want to go deep undercover.
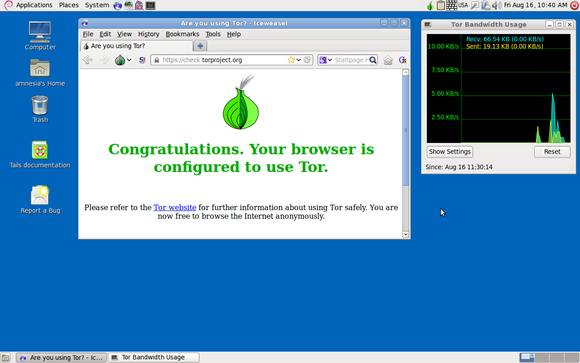
Tails OS: privacy in your pocket
Tails OS is part of the Tor Project, which we discussed earlier. It’s not a web browser like Tor itself, but rather an entire operating system devoted to privacy. You install Tails OS on a DVD or USB drive and run it on any computer you want. Everything needed to run Tails OS stays on the removable disk, and nothing gets written to the computer’s main drives. All data transmitted to and from the computer is filtered through the Tor network, so your browsing activity is completely untraceable, as well. Also, the operating system comes loaded with encryption and secure erase tools, as well as other privacy-oriented software. Think of it as your pocket privacy toolkit.
Stay stealthy
Following these tips is strong first step to reclaiming your privacy. Next, check out our privacy tips for Google, Facebook, and other online services and making your PC Prism proof.
© 1998-2014, IDG Consumer & SMB

No comments:
Post a Comment